Critical infrastructure — energy, water, transport, healthcare, and communications — forms the backbone of modern society. As these sectors digitise operations and integrate IT with operational technology (OT), their exposure to cyber threats has increased significantly.
Cyberattacks on critical infrastructure are no longer hypothetical risks. They are operational realities with national security implications.
A structured, prioritised framework is essential to manage this risk effectively. The CIS Controls provide such a framework — practical, implementation-focused, and proven across industries.
The Problem: Expanding Attack Surface in Critical Infrastructure
Critical infrastructure organisations face a unique challenge:
Legacy OT systems not originally designed for internet connectivity
Convergence of IT and OT environments
Increased remote access and vendor connectivity
Supply chain dependencies
Regulatory pressure and public accountability
Unlike traditional IT breaches, attacks on critical infrastructure can:
Disrupt essential services
Impact public safety
Cause environmental damage
Trigger national-level emergency responses
Operational resilience is therefore not just a cybersecurity objective — it is a societal obligation.
Global Cyberattack Case Studies
1. Colonial Pipeline (USA, 2021)
A ransomware attack disrupted fuel supply across the U.S. East Coast. Although the attack primarily targeted IT systems, operations were shut down as a precaution, demonstrating how IT compromise can affect OT continuity.
Lessons: Asset visibility gaps, weak segmentation, and inadequate incident response readiness amplify operational impact.
2. Ukraine Power Grid Attacks (2015 & 2016)
Sophisticated adversaries compromised energy distribution systems, causing power outages affecting hundreds of thousands of customers.
Lessons: Credential misuse, insufficient network segmentation, and inadequate monitoring allowed attackers to move laterally into control environments.
3. Irish Health Service Executive (2021)
Ransomware crippled healthcare systems, disrupting clinical operations and patient services.
Lessons: Vulnerability management and endpoint hardening weaknesses significantly increase recovery costs and downtime.
https://www.bbc.com/news/world-europe-57184977
These incidents highlight a consistent theme: foundational cybersecurity hygiene failures often enable high-impact operational disruptions.
This is precisely where CIS Controls provide value.
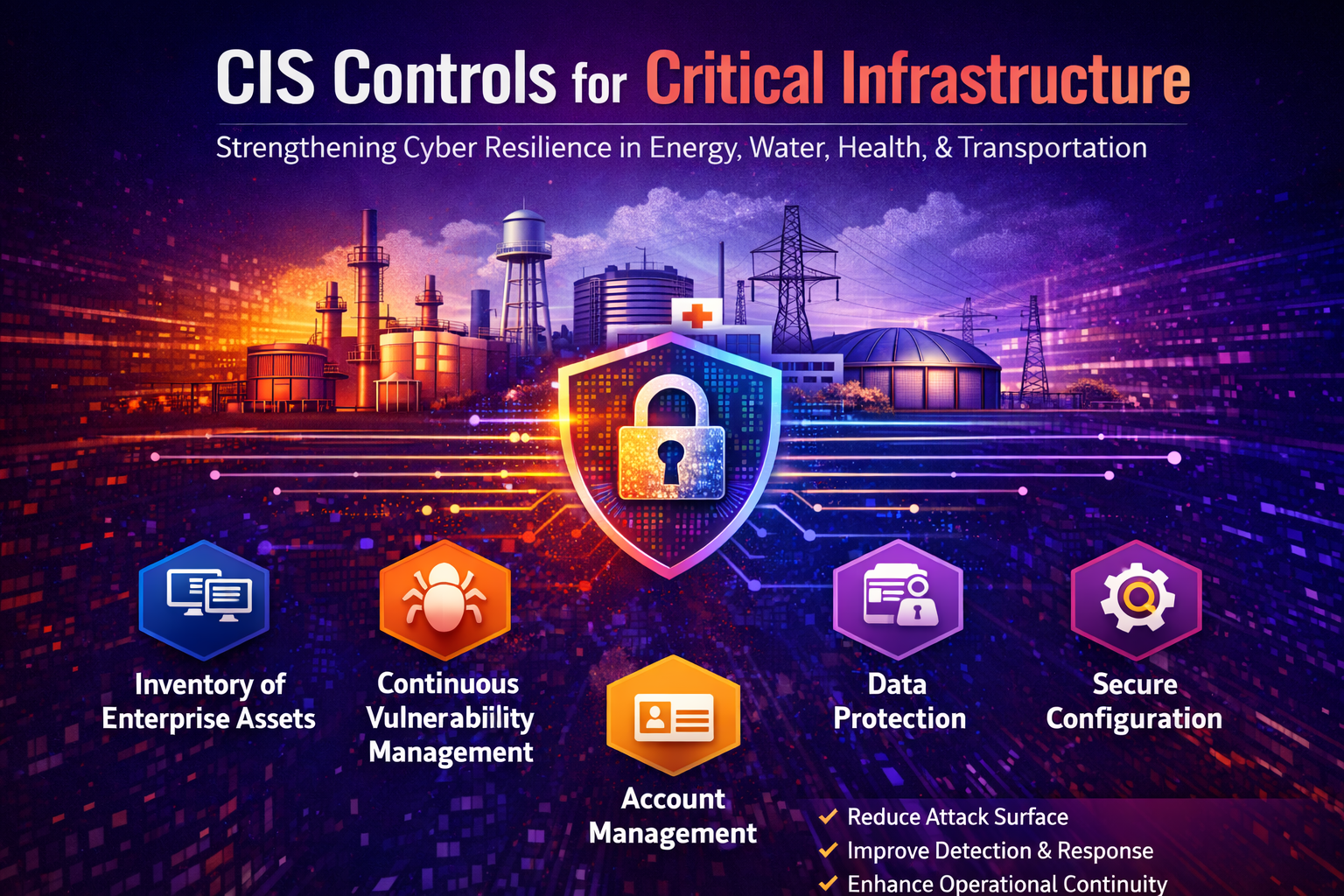
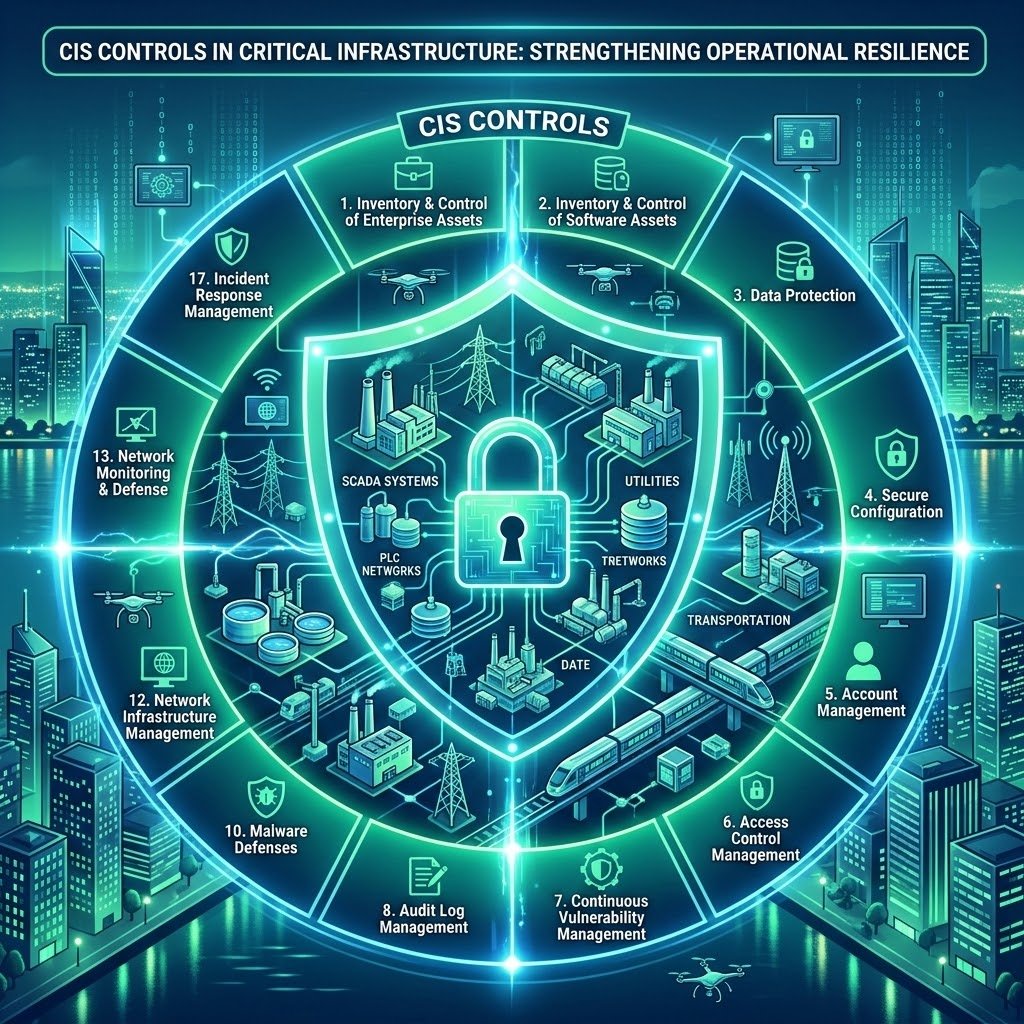
Applying CIS Controls to Critical Infrastructure
The CIS Controls offer prioritised, actionable safeguards that reduce attack surface and strengthen operational resilience.
Below are the most critical controls for infrastructure operators:
1. Inventory and Control of Enterprise Assets
Problem: You cannot protect what you cannot see.
Critical infrastructure environments often contain:
Legacy PLCs and RTUs
Shadow IT systems
Vendor-connected devices
Unmanaged endpoints
CIS Implementation Approach:
Maintain an accurate, continuously updated asset inventory
Classify assets by criticality
Monitor unauthorised device connections
Integrate IT and OT asset visibility tools
Impact: Reduces blind spots and prevents unmanaged assets from becoming entry points.
2. Continuous Vulnerability Management
Problem: Unpatched systems remain the most common attack vector.
In OT environments, patching is complex due to uptime requirements.
CIS Implementation Approach:
Risk-based vulnerability prioritisation
Segmented patch cycles for IT and OT
Compensating controls where patching is not feasible
Regular scanning and validation
Impact: Minimises exploitability without disrupting operational continuity.
3. Data Protection
Problem: Sensitive operational data, configuration files, and engineering documentation are often poorly protected.
CIS Implementation Approach:
Data classification policies
Encryption at rest and in transit
Secure backups (offline and immutable)
Controlled access to configuration repositories
Impact: Protects integrity of operational systems and accelerates recovery after incidents.
4. Secure Configuration of Enterprise Assets
Problem: Default configurations and misconfigured firewalls expose networks to compromise.
CIS Implementation Approach:
Hardened configuration baselines
Removal of unnecessary services
Secure firewall rule reviews
Configuration monitoring for drift detection
Impact: Reduces attack surface and limits lateral movement.
5. Account Management
Problem: Compromised credentials are a primary attack vector in infrastructure breaches.
CIS Implementation Approach:
Centralised identity governance
Privileged access management (PAM)
Multi-factor authentication
Removal of dormant and shared accounts
Impact: Prevents unauthorised access and reduces insider threat risks.
6. Incident Response Management
Problem: Many operators have documentation but lack operational readiness.
CIS Implementation Approach:
Defined incident response playbooks
OT-specific escalation procedures
Tabletop and live simulation exercises
Integration with national cyber authorities
Impact: Reduces downtime, accelerates containment, and improves recovery coordination.
7. Penetration Testing and Red Team Exercises
Problem: Compliance audits do not always reflect real-world attack scenarios.
CIS Implementation Approach:
Periodic penetration testing
OT-aware red team simulations
Attack path validation
Remediation validation testing
Impact: Identifies real exploit chains before adversaries do.
Benefits of Applying CIS Controls in Critical Infrastructure
Implementing CIS Controls enables operators to:
Reduce attack surface and exposure to cyber threats
Improve detection and response capabilities
Enhance continuity of operations
Strengthen resilience across IT-OT convergence
Meet regulatory and compliance obligations
Demonstrate defensible due diligence
Most importantly, CIS Controls are prioritised. They focus on high-impact, high-probability risks first — which is critical in resource-constrained operational environments.
From Compliance to Operational Resilience
Critical infrastructure cybersecurity cannot be reactive or checkbox-driven. It must be structured, measurable, and continuously improved.
CIS Controls provide:
A clear maturity progression path
Practical implementation guidance
Alignment with global best practices
A defensible governance framework
When integrated with sector-specific frameworks and national regulatory requirements, CIS Controls become a powerful foundation for strengthening operational resilience.
Final Thought
Operational resilience is not achieved through advanced tools alone — it is achieved through disciplined implementation of foundational controls.
For critical infrastructure operators, adopting CIS Controls is not simply a cybersecurity improvement initiative. It is a strategic investment in service reliability, public trust, and national stability.
Read more blog articles
https://www.secsolutionshub.com/from-uptime-to-survival-rethinking-industrial-cyber-security/